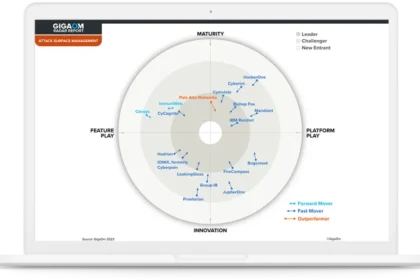
GigaOm Radar for Attack Surface Management 2023 With rapid digital growth, cloud adoption and scattered public IPs and assets, security teams struggle to accurately identify risks. This creates more o...
Approximately 50% of ransomware attacks and breaches fielded by the Unit 42™ Incident Response team result from a common culprit: attack surface exposures. Ransomware is no longer simply about encrypt...
Contain Costs and Reduce Risk with a Strong Cybersecurity Posture The ever-expanding threat landscape keeps evolving, and it is easy to overlook key areas that could expose your organization. However,...
The Strategies to Defend Against Cyberattacks with MITRE ATT&CK The threat landscape is ever evolving. Modern threat actors constantly develop new tactics, techniques and procedures (TTP) so it’s ...
Contain Costs and Reduce Risk with a Strong Cybersecurity Posture The evolution of IT infrastructure, cloud-based applications and cloud-based workloads has elevated the importance of incident readine...
Practical Steps for CISOs to Make Cybersecurity Reporting Frictionless Government-imposed rules on incident reporting by organizations impacted by cyberattacks are not new – many sectors have been sub...
It’s no secret that passwords are a huge security risk, the leading cause of breaches year after year. But they also present a business risk. From forgotten passwords to complex requirements, password...
Having your finger on the pulse of trends helps you make strategic decisions that put you ahead of the competition. None could be more important than eight global digital transformation and consumer t...
An EMEA consumer survey of online behaviour, trust, passwords, and preferences Those of us in cybersecurity spend an inordinate amount of time exploring the best ways to keep people safe online. We kn...
Document automation for law firms can bring a host of benefits — speed, consistency, reduced risk, and less time spent managing changing documents. But how do you get started? Though document automati...