The hybrid work evolution means your business can be conducted everywhere, and threat actors are prepared to take advantage of any holes and gaps in your cyber defenses. Adapting to the world of hybri...
Your Roadmap to a Unified Security Approach By year-end 2028, XDR will be deployed in 30% of end-user organizations to reduce the number of security vendors they have in place, up from less than 5% to...
Experience has taught us all that every system everywhere is either under attack or at least could be. Software applications are one of the primary attack vectors for security breaches. Mitigating the...
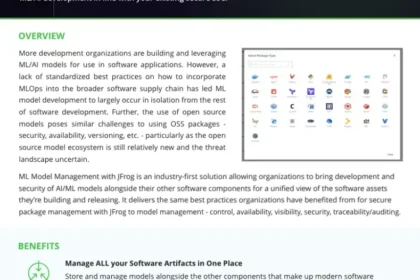
More development organizations are building and leveraging ML/AI models for use in software applications. However, a lack of standardized best practices on how to incorporate MLOps into the broader so...
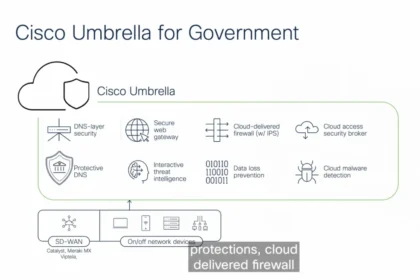
Learn about cyber threat defense for government agencies to protect remote offices and hybrid workers....
How can government agencies, leveraging cloud transformation and hybrid work scenarios for efficiency, engage in their digital transformation without sacrificing security? The answer is Federal Risk a...
Protecting yourself and your business from phishing attacks can be a daunting task. While it’s impossible to eliminate all risk, there are steps you can take to reduce the odds and your brand. Enter “...
Palo Alto Networks continues to redefine the landscape of digital security with Prisma® Access, a leader in delivering consolidated cybersecurity solutions for the modern enterprise. Our steadfast com...
Forrester Has Named Palo Alto Networks a Leader Palo Alto Networks continues to lead the way in transforming digital enterprises through security, networking and IT operations consolidation with Prism...
Cloud and remote work have not only revolutionized the way business is done, but they have irrevocably changed attack surfaces. Assets move, change and appear constantly, and this dynamic nature means...