Unknown assets and cloud dynamism create attack surface risks for all organizations. Understanding these exposures helps security teams shrink their attack surface to proactively secure their organiza...
As the realm of cyberthreats expands, organizations have the difficult task of managing their attack surfaces effectively. Attack surface management enables proactive cybersecurity strategies and miti...
Stop account takeover and new account fraud Evaluate activity before, during, and after login to deliver customized experiences based on the level of risk. Your company can:...
Streamline the verification experience and simplify the admin experience Customers can quickly and securely start engaging with your business. When your customers open an account or engage in a high-r...
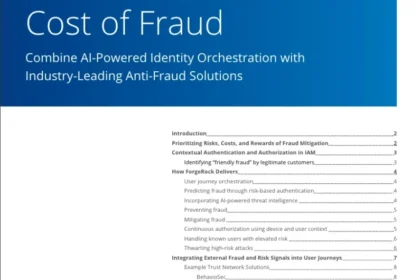
Combine Al-Powered Identity Orchestration with Industry-Leading Anti-Fraud Solutions Digital transformation initiatives offer numerous benefits to organizations, however, following closely on the heel...
Fighting The Next Major Digital Threat: Al and Identity Fraud Protection Take Priority As technology evolves, so does the threat landscape for identity management. Learn why executives are turning to ...
Harness the power of machine intelligence and automation with Cortex XSIAM Security Operations Centres (SOCs) struggle to keep pace with modern threats, the perils of an ever-increasing digital attack...
Large language models (LLMs) work with LLM APIs to unleash the power of generative AI across your organization. MuleSoft’s Universal API Management helps protect and govern any API including LLM APIs ...
The healthcare industry is a common target for bad actors looking to access sensitive patient information, commit insurance or medical identity fraud, or wreak other types of havoc. That means healthc...
Uncover the Costs of Non-Compliance It can be stressful to stay in compliance with changing laws and regulations — especially when non-compliance can lead to steep fines or costly remedies. Know the r...