Ensuring financial compliance with SEC mobile communication record keeping regulations can be difficult, especially with employees using client-preferred communication channels. Join us as we explore ...
Conducting business on mobile devices – e.g., phones and laptops – is a necessity in our industry. However, compliance and security gaps continue to surface, despite compliance policies and data safek...
Please fill this form to get immediate access to this exclusive resource....
Please fill this form to get immediate access to this exclusive resource....
The impact of a security breach in voice communications can cost an organization valuable time and resources to remedy, can lead to damages and even loss of customer loyalty. With the rise in cyber th...
As the threat landscape continues to grow more perilous, enterprise communications security is more critical than ever. Not only are long-standing threats such as toll fraud and telephony denial of se...
Okta commissioned Tech Target’s Enterprise Strategy Group to perform primary research to validate the Workforce Identity Maturity Model. This eBook, and the primary research survey behind it, seeks to...
Company-issued devices are popular once again thanks to increased regulatory needs and more affordable, more reliable international data networks. In this eBook, we look at the growing case against BY...
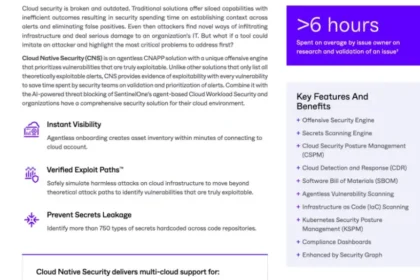
Large Language Models (LLMs) represent a pivotal shift in how enterprises approach innovation, customer engagement, and competitive differentiation. However, the rapid adoption of LLMs also introduces...
See How Palo Alto Networks Performs in the XDR Market “Its company vision — a world where each day is more secure than the one before — aligns with its product vision, a prevention-first approach and ...