What did we learn from our third annual cloud-native security survey? Two themes stand out — life in the cloud does indeed move fast, much faster than we would have imagined 12 months ago. And complex...
While cloud technology is not new, and many organizations have been on the cloud journey for years, cloud service providers continue evolving with new features and services. The fast change and growth...
Implementing an exposure management program enables security professionals to better allocate time and resources so they can focus on taking the actions that legitimately reduce their risk. Read this ...
IN THE 2022 THREAT LANDSCAPE REPORT (TLR), YOU WILL READ ABOUT:...
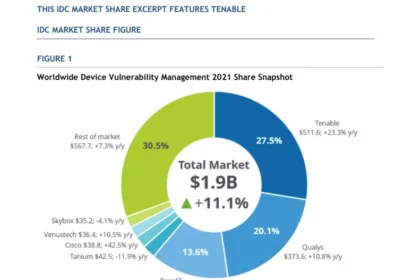
IDC ranks Tenable as #1 in worldwide Device Vulnerability Management 2021 market share for the fourth consecutive year. Want to eliminate blind spots across your entire attack surface, including tradi...
MITRE ATT&CK for ICS is a framework for understanding the tactics and techniques used by threat actors when attacking an industrial control systems (ICS) network. This datasheet covers how Tenable...
Cyberattacks can compromise the ability of water utilities to provide safe water to customers, erode customer confidence, and result in financial and legal liabilities. A robust water system cybersecu...
Cyberattacks are on the rise and the aviation sector is experiencing growing interest among cyber criminals. On March 7, 2023, the TSA updated their cybersecurity requirements for airports and aircraf...
Explore the security risks and best practices for adopting connected technologies on the manufacturing floor in this white paper. Tenable OT Security enables manufacturers to detect threats and respon...
To protect people, data, and production machinery, manufacturers need a comprehensive cybersecurity strategy. This requires adopting best practices and complying with industry standards and regulation...