Egress security in the public cloud comprises a significant portion of the total security posture toward protecting public cloud workloads. Cisco Multicloud Defense is architected using software-defin...
Tobacco and vape organizations have many environmental, health, and business standards to meet, and managing compliance against these regulations can be challenging. This report analyzes how leading o...
As cyberattacks become more sophisticated, securing networks and applications becomes more challenging. Preparation is key to help your organization prevent and protect against evolving threats. Apply...
While Kubernetes built-in security solutions do not cover all potential issues, there is no shortage of security solutions within the Kubernetes ecosystem. While a number of Kubernetes security ...
Get your secrets into one central tool or platform. Some might see it as counterintuitive to have one place where attackers know they can find your secrets, but it’s actually much safer to harden one ...
The way organizations provision infrastructure has significantly changed as they move from dedicated servers to capacity on-demand in the cloud. Homogeneous blueprints of infrastructure owned by IT ha...
Over 5,500 physical security end users and channel partners worldwide were surveyed. Find out what your peers said about top trends in 2024. Each year, Genetec surveys physical security professionals ...
The CMMC represents a critical mandate from the U.S. DOD. Aerospace & Defense manufacturers that handle controlled unclassified information (CUI) must comply with CMMC requirements or risk losing ...
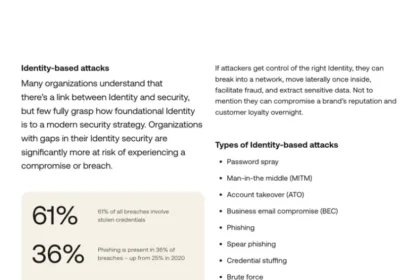
Many organizations understand that there’s a link between Identity and security, but few fully grasp how foundational Identity is to a modern security strategy. Organizations with gaps in their Identi...
As a security practitioner, protecting your organization’s data is your number one priority. Yet with the explosion of the mobile and hybrid workforce, SaaS adoption, and application modernization, ne...