Did you know that 66% of organizations were hit with a ransomware attack last year? If your business relies on Microsoft 365 for day-to-day business, it is extremely attractive for cybercriminals due ...
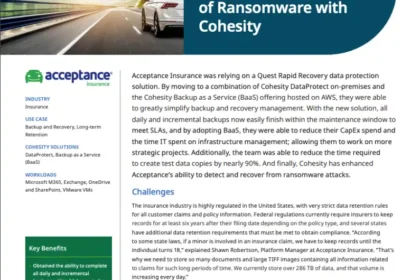
With SOX compliance and state insurance regulations, Acceptance Insurance was bleeding resources, time, and money to keep up. They also had a lot of issues around expansion flexibility and security on...
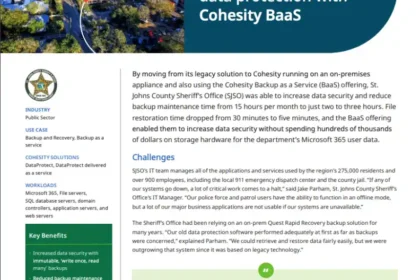
If 911 goes down, people’s lives are at stake. And if valuable user data was compromised in a ransomware attack, that could be devastating to the community. That’s why St. John’s County Sheriff’s Offi...
Driven by the rise in remote work, increased automation and shifting customer expectations, financial services organizations increasingly turn to UCC solutions to unlock organizational agility. Our eB...
The internet of things (IoT) affords us connectivity and convenience, but it presents enterprises with an inconvenient truth: IoT and OT devices are prime targets for cyberattacks. The Zscaler ThreatL...
With users and applications anywhere and everywhere, organizations are looking at new, more efficient ways to protect their users and sensitive data. Secure access service edge (SASE) models are drawi...
Evolve your security strategy with AI-powered threat protection. When your digital world contains valuable assets and sensitive data, adversaries are on the hunt for security gaps to execute devious a...
Enterprises worldwide are racing to speed up innovation while becoming more agile and competitive. To do that while securing users, workloads, and devices in modern environments, IT leaders agree they...
The 10 Must-Have Capabilities of an Effective ZTNA Solution The way we work has undeniably changed. As organizations embrace hybrid work, while also considering return to office, they’re moving growin...
The transformation of hybrid work, cloud adoption, and zero trust environments has increased pressure for network and service desk teams to ensure fast and secure access to resources. The added comple...