Cybersecurity breaches are inevitable. Instead of striving to prevent breaches, focus on resilience and embrace hacks as incidents to learn from. Read the Gartner Maverick* Research: You Will Be Hacke...
Security is a journey, and adopting a Zero Trust approach is one of your best defenses against attackers. See how Veeam Data Platform can help you move closer to radical resilience and meet your compl...
Security is a journey, and adopting a Zero Trust approach is one of your best defenses against attackers. See how Veeam Data Platform can help you move closer to radical resilience and meet your compl...
Every minute of downtime can mean thousands of dollars in lost business. When ransomware hits, paying the ransom can be tempting, but it isn’t the quick fix organizations are hoping for. Instead, ente...
Read how special operations forces can improve security posture and cyber resilience by scaling automation with Red Hat Ansible Automation Platform....
Industry standards help set the foundation for a safety management system (SMS) that protects workers, but data gathering is the engine that drives it. The Intelex Insight Report “Safety Management Sy...
Dive into the data for a complete picture of the state of DevSecOps in 2023. How are DevSecOps teams using artificial intelligence (AI) in software development today, and where do they actually want t...
Get the Complete Code to Cloud CybersecuritySummit Library Code to Cloud Cybersecurity Summit is your great leap forward: Made for practitioners by practitioners, it features tactical how-tos and visi...
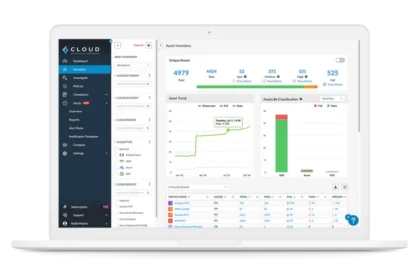
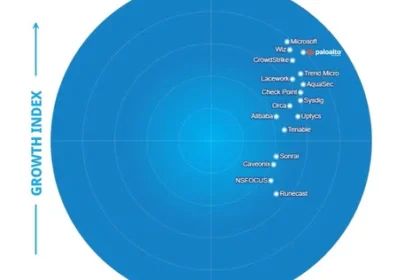
A Leader Positioned the Furthest on Innovation With the emergence of cloud-native application protection platforms, more than 30 cybersecurity companies have been fast at work creating a solution in t...
Zero Trust Holds the Key to Cloud and Application Security Can you protect all clouds — private, public, hybrid — with the agility your business needs to stay competitive? Read this in-depth whitepape...